
Managing Third-Party Data Privacy Risks: Understanding Data Sharing and Outsourcing Agreements
Third-party relationships are essential for growth and efficiency. However, these partnerships often involve the exchange of personal data, making data privacy a critical concern. Without proper safeguards, businesses risk exposing themselves to regulatory penalties, legal liabilities, and reputational damage.
This is where data sharing and outsourcing agreements come into play by providing a structured framework to ensure compliance with data privacy laws and protect the confidentiality, integrity, and availability of personal data. This guide dives into the nuances of data sharing and outsourcing agreements, offering practical insights and actionable steps to help your business navigate third-party data privacy risks effectively.
- Why Third-Party Relationships Create Data Privacy Risk
- Third-Party Risk Management in Data Privacy Compliance
- Data Sharing Agreements under NPC Circular No. 2020-03
- Comparing Data Sharing and Outsourcing Agreements
- Key Considerations in Executing Data Privacy Agreements
- Practical Steps Your Business Can Take
- Frequently Asked Questions
Why Third-Party Relationships Create Data Privacy Risk
Business organizations increasingly rely on third-party vendors, service providers, consultants, and technology partners in their day-to-day operations. Such relationships often involve the transfer or disclosure of personal data.
Under the Philippine Data Privacy Act of 2012 (DPA), Personal Information Controllers (PICs) remain accountable for the personal data they control, even when processing is performed by third parties.
Not having contractual safeguards in place can potentially expose such businesses to regulatory, legal, and reputational risks.
Third-Party Risk Management in Data Privacy Compliance
Vendors and other third parties collect, use, access, and store personal data.
Possible risks arise from these data processing such as:
- Unauthorized disclosure to other persons or entities that should have no access to information.
- Improper processing of data that could pose a risk to individuals whose information is handled.
- Cross-border data transfers with insufficient security measures and poorly designed mechanisms to protect personal data.
- Data breaches that compromise the confidentiality, integrity, and accessibility of sensitive personal information.
The National Privacy Commission (NPC) mandates business organizations to come up with clear contractual frameworks that are meant to govern data processing relationships.
Two contractual mechanisms under our local regulations are the Data Sharing Agreement (DSA) and the Outsourcing Agreement.
Data Sharing Agreements under NPC Circular No. 2020-03
What is a Data Sharing Agreement?
The DSA is executed to govern the sharing of personal data between two or more Personal Information Controllers (PICs).
In such a situation, these parties determine the purpose and means of processing where personally identifiable information is shared between such organizations.
To illustrate this, financial institutions share data to prevent fraud. Affiliate companies share customer information. Private sector companies collaborate on mutual business endeavors.
The contractual agreement ensures that all parties clearly set forth and understand their obligations in protecting the personal data they handle.
Outsourcing Agreements under the DPA Implementing Rules and Regulations (Rule X, Sections 43 to 45)
What is an Outsourcing Agreement?
Under Section 43 of the IRR, a PIC may outsource or subcontract the processing of personal data, provided that the PIC uses contractual or other reasonable means to ensure that adequate measures are in place to secure the confidentiality, integrity and availability of the personal data processed, and prevent its use for unauthorized purposes.
As a best practice, many companies engage in the services of payroll providers, cloud storage providers, HR management solutions providers, IT service providers, and customer support vendors, to name a few, so they can focus on their core business operations.
In such a scenario, the PIC retains its responsibility for ensuring compliance with the DPA, even when processing is delegated to a Personal Information Processor (PIP).
The provisions of the Outsourcing Agreement help ensure that PIPs handle personal data in compliance with data privacy regulations, and that the PIP has the capability to demonstrate a comparable level of protection in relation to personal data processing.
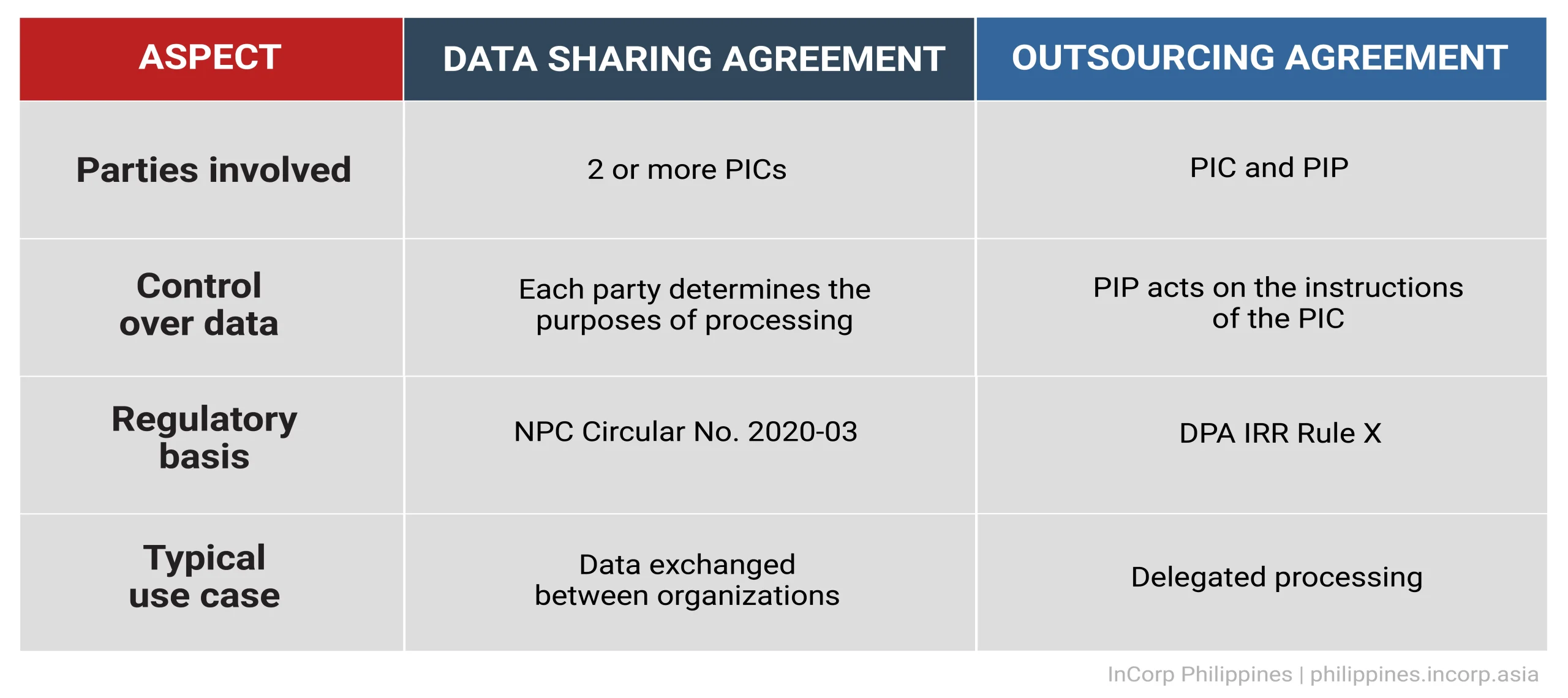
Comparing Data Sharing and Outsourcing Agreements
Key Considerations in Executing Data Privacy Agreements
You may consider these factors when implementing contractual relationships with third parties:
- Data breach response coordination
The contract should contain protocols that both parties are to adopt when a privacy incident occurs, including establishing internal timeframes for the processor to notify the PIC that such an incident has taken place.
Keep in mind that NPC regulations require PICs to duly notify such a regulator within a 72-hour timeline upon knowledge of or reasonable belief that a breach has happened. Notification to affected data subjects must also be done.
- Cross-border data transfer safeguards
Transfer takes place when personal data is shared with other parties outside of a certain geographical jurisdiction. Safeguards or security measures must be properly adopted.
- Map where your data is situated and where it is transferred to
- Identify the mechanisms used for such transfer
- Assess how effective such transfer mechanisms are
- Make use of additional safeguards when needed
- Make sure that the additional security measures align with actual business requirements
- Perform regular compliance monitoring
- Vendor due diligence
Vendor risk management, also known as third-party risk management, is considered a prevalent topic in the business community nowadays. A business will need to procure products or raw materials to sustain its operations. There is a need to make sure that data will remain secure and protected.
A business may take the following steps to manage potential privacy risks:
- Know your vendors and their legal obligations
- Assess risks, policies, and server locations
- Develop adequate contracts
- Monitor their practices and how they perform over time
- Adopt a vendor policy
Practical Steps Your Business Can Take
Businesses can take the following steps moving forward:
- Make an inventory of all vendors and business partners that have access to your personal data.
- Determine the business relationship that exists (data sharing versus outsourcing).
- Conduct vendor privacy due diligence. Vet out your vendors and service providers before onboarding them.
- Implement appropriate contractual agreements.
- Periodically review third-party compliance with DPA regulations.
As organizations increasingly work with third-party partners and service providers, strong contractual safeguards become highly crucial. Executing properly structured Data Sharing Agreements and Outsourcing Agreements helps ensure compliance with DPA regulations and strengthens a company’s overall third-party risk management strategy.
Frequently Asked Questions in Managing Third-Party Data Privacy Risks in the Philippines
Why are third-party relationships a data privacy risk?
Third-party relationships often involve sharing and processing personal data. Without proper safeguards, businesses risk unauthorized disclosures, improper data handling, cross-border data transfer vulnerabilities, and data breaches, which can lead to regulatory, legal, and reputational consequences.
What is the difference between a Data Sharing Agreement (DSA) and an Outsourcing Agreement?
A DSA governs the sharing of personal data between two or more Personal Information Controllers (PICs), where each party determines the purpose and means of processing. An Outsourcing Agreement, on the other hand, involves a PIC delegating data processing to a Personal Information Processor (PIP), who acts solely on the PIC’s instructions.
What are the key considerations when executing data privacy agreements?
Key considerations include establishing data breach response protocols, ensuring cross-border data transfer safeguards, conducting vendor due diligence, and implementing clear contractual terms to define responsibilities and compliance requirements.
How does the Philippine Data Privacy Act (DPA) regulate third-party data processing?
Under the DPA, Personal Information Controllers (PICs) remain accountable for personal data, even when processing is outsourced or delegated to third parties. The law mandates the use of contractual agreements, such as Outsourcing Agreements, to ensure compliance and protect data integrity. Data Sharing Agreements, on the other hand, are business best practices you may implement to ensure personally identifiable information shared between two Personal Information Controllers (PICs) is properly protected.
What practical steps can businesses take to manage third-party data privacy risks?
Businesses should perform an inventory of all its vendors with access to personal data, determine the nature of their relationships (data sharing vs. outsourcing), conduct vendor privacy due diligence, implement appropriate agreements and adequate security measures, and regularly review third-party compliance with DPA regulations.


